Technology
Chainiste Unveiled: The Next Big Thing in Tech?

In the ever-evolving world of technology and fashion, a new trend is making waves: Chainiste. This captivating fusion of chains and textiles is not just a fashion statement but a symbol of how traditional art forms are merging with cutting-edge technology. Chainiste is more than a style; it’s a digital platform that leverages blockchain technology to decentralize and revolutionize both the world of jewelry craft and the realm of digital assets.
The Emergence of Chainiste
Defining Chainiste:
Chainiste lies at the intersection of artistry and technology. It is a unique style characterized by the intricate weaving of chains into clothing and accessories, creating an eclectic and personalized look. This style is not just limited to jewelry like bracelets and necklaces but extends to a complete head-to-toe Chainiste look. Historically, Chainiste has roots in various cultures, and its revival in the 1960s marked a golden age that continues to inspire contemporary designers.
Chainiste in Jewelry:
The beauty of Chainiste lies in its versatility and the endless possibilities it offers for creativity. Artisans can start with basic materials like sterling silver or gemstones to create eye-catching pieces. The craft results in anything from subtle bracelets in earthy tones to bold necklaces that make a statement. The Chainiste style is not limited by your imagination, with each piece reflecting a unique blend of experimentation and creativity.
Chainiste and Blockchain Technology
Leveraging Blockchain for Managing and Exchanging Digital Assets
Chainiste is not just about physical art; it’s also a digital platform that leverages blockchain technology. This platform allows artists and businesses of all sizes to manage and exchange digital assets securely. By eliminating the need for intermediaries, Chainiste offers a decentralized approach, empowering users within the platform to have more control and transparency over their digital transactions.
Best Practices in Chainiste Fashion and Technology
Chainiste offers a unique opportunity to merge the worlds of art and blockchain. On the fashion front, mastering the Chainiste look involves combining different elements like chain stitching on clothing with modern aesthetics. In terms of technology, the platform adheres to best practices in blockchain, ensuring that all transactions are secure and efficient, pushing the boundaries of how digital platforms can support traditional art forms.
The Future of Chainiste
Captivating Fusion of Chains and Textiles
Chainiste fashion continues to captivate with its fusion of chains and textiles. From the historical significance of Chainiste fashion to the modern Chainiste look, this style has taken the nation by storm. Chainiste allows crafters and makers to explore their creativity by weaving chains into various forms, be it clothing, jewelry, or accessories. The allure of this ornate and industrial style creates an edgy vibe that is effortlessly appealing.
Chainiste’s Role in Supply Chains and Digital Platforms
In the realm of technology, Chainiste provides an innovative approach to managing supply chains and digital assets. The platform leverages the power of blockchain technology to offer a wide range of features for businesses and individuals. This includes secure transactions, a decentralized system, and the potential for integrating Chainiste fashion into the digital world, reaching a wider audience and creating new opportunities for artists and entrepreneurs.
Read more information about here: https://blogtimes.net/
Conclusion
Chainiste stands as a symbol of the fusion between the old and the new, the traditional and the modern. As a style, it continues to inspire with its unique and unconventional approach to fashion. As a technology, it represents the future of digital platforms, combining the security and efficiency of blockchain with the creativity and artistry of fashion. Whether you’re a seasoned artisan or a tech enthusiast, Chainiste offers a realm where you can delve into the world of jewelry, art, and digital innovation, redefining what it means to be at the forefront of technology and style.
new
The Allure and Intrigue of Cursed Text: Understanding Curse Dtext

Introduction
In the great panorama of virtual conversation, styles of expression are continuously evolving, reflecting shifts in subculture, era, and aesthetics. One of the maximum fascinating phenomena in recent years is the upward push of “cursed text” or “curse text.” This stylized writing, characterized by its distorted and chaotic appearance, serves as a visual representation of a particular subculture inside the net. This article will discover the origins, uses, and cultural implications of curse textual content, as well as its aesthetic appeal and a way to create it.
Table of Contents
What is Cursed Text?
The Origins of Cursed Text
How to Create Cursed Text
Online Generators
Manual Creation
Cultural Significance of Cursed Text
Cursed Text in Memes and Social Media
Psychological Impact of Cursed Text
Examples of Cursed Text
Cursed Text in Art and Literature
Critiques and Concerns
Readability Issues
Misuse and Trolling
Conclusion
FAQs about Curse Text

1. What is Cursed Text?
Cursed textual content, frequently known as glitch text, void textual content, or demonic text, involves the usage of Unicode diacritics and different symbols to create an unsettling or distorted appearance. This shape of writing performs with typography to evoke feelings of chaos and confusion. The textual content often appears even though it’s been corrupted or hacked, making it difficult to read and lending a creepy aesthetic to the words.
The period “cursed” in this context does not suggest a real curse but as an alternative shows a playful engagement with the darker, extra-chaotic factors of a virtual lifestyle. Users often utilize cursed text to deliver emotions or concepts that align with horror, chaos, or the surreal.
2. The Origins of Cursed Text
The origins of cursed text may be traced again to the early days of net way of life, mainly in the nation-states of gaming and online forums. The concept gained traction alongside the improvement of the meme way of life, in which users began to test textual content styles to create funny or unsettling consequences. Curse text became a way to explicit absurdity and chaos in a visible format, appealing to the developing net culture that revels in the bizarre and uncanny.
The upward thrust of social media structures further propelled the recognition of cursed text. As users sought precise methods to stand out and express their individuality, the use of glitchy, distorted textual content became a favored technique of verbal exchange. It is especially popular on systems like Tumblr, Twitter, and TikTok, wherein customers often publish content that demands conventional aesthetics.
3. How to Create Cursed Text
Online Generators
Creating cursed textual content has in no way been easier, thanks to quite a few online equipment and turbines. These structures allow customers to enter trendy textual content and receive a stylized output in real time. Some popular mills consist of:
LingoJam Cursed Text Generator: This user-friendly tool offers a couple of styles of cursed textual content via manipulating Unicode characters, allowing customers to see actual-time effects as they kind.
Glitch Text Generator: Similar to LingoJam, this generator lets customers create numerous glitchy text styles, frequently referred to as “Zalgo” text, which appears to drip or bleed, enhancing the chaotic aesthetic.

Manual Creation
For people who opt for a hands-on method, curse textual content also can be created manually. By using Unicode diacritic marks, customers can layer them over letters to acquire the preferred effect. This technique involves information as a way to integrate numerous characters correctly, creating a text that resembles a glitch or distortion.
While this approach can be extra time-eating, it allows for greater customization and creativity. Resources that include Unicode charts can assist in deciding on the right characters for developing precise cursed text styles.
4. Cultural Significance of Cursed Text
Cursed Text in Memes and Social Media
Curse text has become a staple of internet memes, often used to bring absurdity, humor, or horror. It provides a visual illustration of emotions that may be hard to articulate in preferred text, allowing users to speak in a way that resonates with their audience. The chaotic nature of cursed textual content enhances the message, making it extra impactful.
5. Examples of Cursed Text
Cursed textual content can take many forms, each with its precise appeal. Some examples include:
Zalgo Text: This fashion is characterized by text that looks to be corrupted or distorted, regularly used to bring an experience of horror or the supernatural. For example, the word “Help me” might also seem as “H̴̡̀e̴̢͝l̸̙̿p̵͆͜ ̶̖̈́m̵̼̍e̵̮̿.”
Glitch Text: Similar to Zalgo text, glitch text frequently features overlapping characters and logos, developing a sense of disarray. An instance can be “Glitchy t̸͔͐e̴͉͆x̷̠̄t̴̪͌.”
Void Text: This style emphasizes emptiness or loss, regularly used in artistic expressions to awaken feelings of despair or existential dread. An instance is probably “Ṫ̶͍h̵͍͆e̸̗̔ ̶̝́v̸͍̆o̶̖͐ḯ̶̼d̵̦̋.”
These examples illustrate how curse text can be applied creatively across exceptional contexts, from memes to creative expressions.
6. Cursed Text in Art and Literature
Beyond memes and social media, the cursed text has determined its way into various varieties of artwork and literature. Artists and writers have started to include curse textual content into their works, using its chaotic aesthetic to beautify issues of misunderstanding, alienation, or the uncanny.
Visual artists might also use curse text as a part of blended-media installations, combining it with different types of expression to create a disorienting reveal in for visitors. Similarly, writers can also appoint cursed text in virtual storytelling, the use of it to bring feelings or subject matters that resonate with the reader’s experiences in a chaotic international.
The integration of cursed textual content into artwork and literature highlights its potential as a powerful tool for communication, permitting creators to interact with audiences to a deeper degree.
Critiques and Concerns
Readability Issues
Despite its popularity, cursed textual content isn’t always without its evaluations. One of the primary worries is its impact on readability. The distorted nature of the cursed text can make it challenging to apprehend, leading to frustration among readers. While a few customers may additionally recognize the culture, others argue that clarity ought to take precedence, particularly in kinds of communique wherein comprehension is vital.

Misuse and Trolling
Cursed textual content has additionally been related to bad behaviors, including trolling or harassment. Some individuals use cursed text to disrupt conversations or initiate reactions from others, often leading to misunderstandings or struggles. This misuse increases issues about the wider implications of cursed text in online interactions, as it may contribute to toxic digital surroundings.
Read more information about here: Adrienne Calhoun: The Life of George Foreman’s First Wife
Conclusion
Cursed textual content represents a fascinating intersection of digital tradition, aesthetics, and communique. Its potential to evoke emotion and produce complex subject matters through distorted typography has captured the imagination of internet customers globally. While it serves as a playful engagement with chaos, cursed textual content additionally raises important questions on clarity and its capability for misuse.
As we navigate the evolving landscape of digital expression, curse text remains a powerful reminder of the internet’s ability for creativity and absurdity. It invitations users to explore the limits of language and aesthetics, offering a completely unique lens via which to view contemporary communique.
FAQs approximately Cursed Text
Q: What is cursed textual content?
Cursed text, or curse text, refers to a shape of stylized writing that uses Unicode diacritics and logos to create a distorted, chaotic look. It often conveys problem subjects of horror or absurdity.
Q: How can I create cursed text?
You can create curse textual content with the use of online turbines like LingoJam’s Curse Text Generator or Glitch Text Generator, or with the useful resource of manually layering Unicode characters over letters.
Q: Why is cursed textual content well-known?
Cursed text has gained a reputation due to its particular aesthetic, its ability to hold complex emotions, and its feature in meme tradition. It resonates with internet customers who recognize its absurd and chaotic nature.
Q: Are there any issues approximately the usage of cursed text?
Yes, some evaluations are aware of readability troubles, as curse textual content can be difficult to understand. Additionally, it can be misused for trolling or harassment, contributing to poor online interactions.
Q: WhereQ: Where can I see examples of cursed textual content?**
You can find examples of cursed text in numerous meme codecs on social media structures like Twitter and TikTok, in addition to precise meme companies on Reddit. Additionally, online turbines like LingoJam and Glitch Text Generator can display actual-time examples as you create curse text.
Q: Is cursed textual content utilized in professional contexts?
While curse textual content extensively flourishes in informal and meme-pushed spaces, it has additionally been used in artistic initiatives and virtual storytelling. However, it is commonly no longer appropriate for expert or formal verbal exchange due to its chaotic nature.
Q: What is the future of curse textual content?
As digital verbal exchange continues to adapt, curse textual content can also find new expressions and variations. Its potential to resonate with topics of chaos and absurdity ensures it’ll stay a relevant issue of the net way of life for the foreseeable future.
Technology
The Imalent MS32: Illuminating the Path to Power and Performance

The Imalent MS32 is a current tactical flashlight that mixes powerful illumination with a compact layout, making it a vital tool for outdoor fanatics, experts, and emergency preparedness. In this text, we can discover the functions, specifications, benefits, and actual worldwide packages of the Imalent MS32.
Introduction
In a global wherein dependable light sources are critical, the Imalent MS32 sticks out for its wonderful brightness, durability, and versatility. Whether you’re navigating through the wasteland, carrying out search and rescue operations, or need a dependable mild for ordinary use, the MS32 is designed to satisfy your light desires.

Key Features of the Imalent MS32
1. Unmatched Brightness
The Imalent MS32 boasts a fantastic output of sixteen,000 lumens, making it one of the brightest flashlights available. This extremely good brightness permits customers to light up large areas and notice items at extremely good distances, ensuring visibility in even the darkest environments.
2. Multiple Lighting Modes
The MS32 features six brightness tiers, together with:
Turbo Mode (sixteen,000 lumens)
High Mode (eight,000 lumens)
Medium Mode (3,500 lumens)
Low Mode (12 hundred lumens)
Eco Mode (one hundred lumens)
Strobe and SOS Modes
These options provide flexibility for diverse situations, permitting users to preserve battery lifestyles or maximize brightness as wanted.
3. Efficient Cooling System
To hold the most appropriate overall performance and save you from overheating all through extended use, the Imalent MS32 is prepared with an advanced cooling device. This guarantees that the flashlight can preserve excessive output without compromising protection or efficiency.
4. Built-In Rechargeable Battery
The MS32 comes with an integrated battery percent that can be without difficulty recharged through a USB-C port. This feature gets rid of the want for disposable batteries and ensures that the flashlight is usually ready for movement. The battery can offer as much as 48 hours of continuous use on lower settings.
5. Durable Construction
Constructed from splendid aerospace-grade aluminum, the MS32 is lightweight and robust. It is designed to face up to harsh conditions, making it appropriate for outdoor adventures and emergencies. Additionally, the flashlight is rated IPX-8, which means it has miles of water evidence and might withstand immersion in water up to 2 meters.

6. Compact and Portable Design
Despite its effective skills, the MS32 remains compact and transportable, making it smooth to carry in a backpack, glove compartment, or pocket. Its ergonomic layout ensures a comfortable grip, even at some stage in extended use.
Specifications of the Imalent MS32
Specification Details
Max Output 16,000 lumens
Battery Built-in rechargeable lithium-ion battery
Charging Port USB-C
Material Aerospace-grade aluminum
Water Resistance IPX-eight (water-resistant as much as 2m)
Dimensions five.Eight x 2.Five x 2.Five inches
Weight Approximately zero.86 lbs
Runtime Up to forty-eight hours on Eco mode
Benefits of Using the Imalent MS32
1. Versatile Applications
The Imalent MS32 is right for a wide variety of sports, which includes:
Camping and Hiking: Its effective illumination makes navigating trails and putting in place camp at night time a great deal less complicated.
Search and Rescue: The excessive brightness and numerous modes allow for effective signaling and visibility at some point in emergencies.
Everyday Use: Perfect for domestic use, protection patrols, and outside activities.
2. Cost-Effective
The integrated rechargeable battery reduces long-term charges associated with buying disposable batteries. The flashlight’s sturdiness additionally approaches it can withstand the trials of outside use, presenting notable cost for money.
3. User-Friendly Features
With intuitive controls and more than one brightness setting, the MS32 is simple to perform, even for novices. The built-in charging port adds convenience, making sure that users can recharge the flashlight fast while wishing.

Real-World Applications
1. Outdoor Adventures
For campers and hikers, the Imalent MS32 offers peace of thoughts in the course of midnight excursions. Its immoderate lumen output ensures that even the darkest paths are illuminated, thinking of safe navigation and exploration.
2. Emergency Preparedness
In emergencies, having a dependable flashlight is important. The MS32’s various modes, including strobe and SOS, may be vital for signaling for assisting or illuminating dark regions through energy outages.
3. Professional Use
Law enforcement, firefighters, and protection employees can experience the MS32’s immoderate brightness and durability. It is an important device for carrying out searches, investigating suspicious activity, or imparting illumination in low-light conditions.
Read more information about here: Bess Katramados: The Woman Behind WWE’s Big Show
Conclusion
The Imalent MS32 is a pinnacle-tier flashlight that combines super brightness, durability, and versatility, making it a crucial tool for everybody in want of a dependable light supply. Whether for outdoor adventures, emergency preparedness, or professional applications, the MS32 offers overall performance and functions that cater to a wide range of wishes. With its purchaser-friendly layout and incorporated rechargeable battery, the Imalent MS32 stands out as an investment in protection and comfort.
FAQ
1. What is the most output of the Imalent MS32?
The Imalent MS32 has the most output of 16,000 lumens.
2. How lengthy is the battery final?
The battery can offer as much as 48 hours of runtime in Eco mode, depending on the brightness used.
3. Is the Imalent MS32 waterproof?
Yes, the MS32 has an IPX-eight rating, which means it’s miles water-proof and may withstand immersion in water up to 2 meters.
4. How do I recharge the Imalent MS32?
The flashlight can be recharged via a USB-C port for available charging.
5. What materials is the MS32 manufactured from?
The Imalent MS32 is crafted from aerospace-grade aluminum, ensuring sturdiness and a lightweight introduction.
new
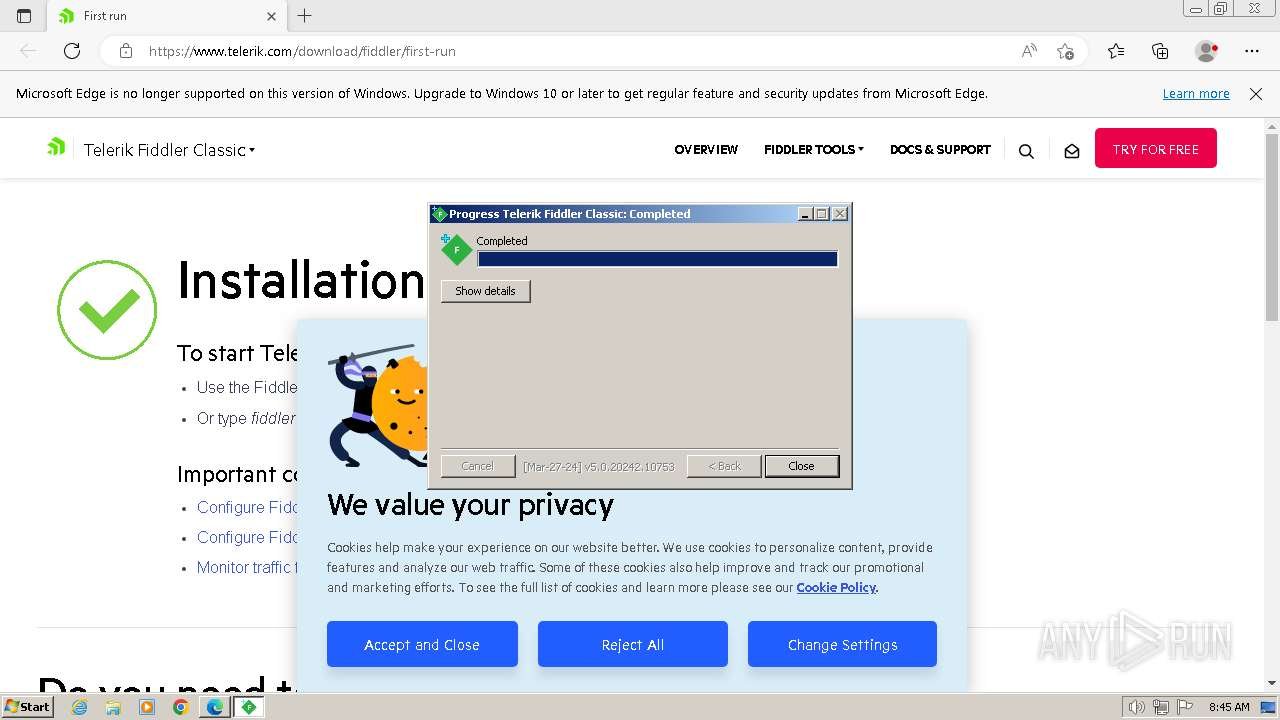
Using Fiddler Without Admin Rights: A Comprehensive Guide
Introduction
Fiddler is a powerful internet debugging proxy tool that allows builders, testers, and IT professionals to capture, investigate, and control HTTP and HTTPS traffic among patron applications and internet servers. It is typically used to reveal website visitors, become aware of performance bottlenecks, and debug troubles in internet packages. While it is exceedingly easy to apply, it normally requires administrative rights to modify system-huge proxy settings and set up root certificates for HTTPS site visitors’ inspection.
For customers in environments where administrative privileges are confined, consisting of corporate networks, jogging it without admin rights may be difficult. However, there are methods to paint around those limitations. In this newsletter, we’ll discover how you could run it without admin rights, its benefits, limitations, and sensible hints to make the maximum out of it.
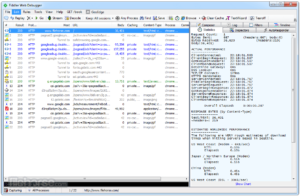
What is Fiddler?
Fiddler is a web proxy device evolved using Telerik that captures HTTP and HTTPS visitors. It lets users look into requests and responses, permitting them to analyze how internet packages communicate with servers. It’s often used for debugging web packages, overall performance testing, and protection testing using developers, quality warranty testers, and IT experts.
Key Features of Fiddler:
Traffic Capture: Fiddler captures all HTTP and HTTPS visitors among the person’s gadget and web servers, enabling specific evaluation of requests and responses.
The decryption of HTTPS Traffic: Fiddler can decrypt HTTPS traffic by putting in a root certificate, allowing users to view touchy records, inclusive of cookies, headers, and shape fields.
Traffic Manipulation: Users can adjust HTTP requests and responses on the fly, which is useful for debugging APIs and trying out security features.
Performance Testing: Fiddler offers insights into reaction times, helping builders optimize the overall performance of their programs.
Security Testing: By intercepting and manipulating HTTP site visitors, users can take a look at vulnerabilities, such as go-web page scripting (XSS) and injection attacks.
Why Fiddler Requires Admin Rights
To characteristic nicely, It wishes to set itself because the machine’s proxy server intercepts all web visitors. It additionally calls for putting in a root certificate to inspect HTTPS traffic, as encrypted conversation needs to be decrypted for analysis. Both of those operations generally require admin rights. However, in environments wherein users aren’t allowed to have admin rights, inclusive in corporate settings or academic institutions, the usage of Fiddler may be tricky.
Fortunately, there are ways to use it without admin privileges. Below are numerous strategies that permit customers to run it in restricted environments.

How to Use Fiddler Without Admin Rights
1. Running Portable Fiddler
One method for using Fiddler without admin rights is to run a transportable model of the software. A transportable software does now not require installation and can run from any vicinity of the file device, which includes external drives.
While it no longer officially offers a transportable model, users can create their own with the aid of copying the installed files from a machine with admin rights and shifting them to the target device. Here’s how:
1. Install Fiddler on a gadget with admin rights.
2. Copy the established documents (typically positioned within the “Program Files” folder).
3. Transfer the documents to the gadget without admin rights, and run Fiddler from the copied listing.
This technique avoids the need for installation but may additionally nevertheless require proxy configuration at the browser manually.
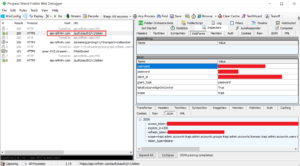
2. Manually Configuring Browser Proxy Settings
Even without admin rights, you could configure your browser’s proxy settings manually to path visitors through Fiddler. Here’s a step-by means of-step guide:
Open Fiddler: Launch Fiddler as a normal consumer (without admin rights).
Find Fiddler’s Listening Port: Go to Tools > Options > Connections. Note the port quantity Fiddler is the usage of (default is 8888).
Set Browser Proxy:
For Chrome: Go to Settings > Advanced > System > Open your computer’s proxy settings.
For Firefox: Go to Settings > General > Network Settings > Settings.
For Edge: Go to Settings > System > Open your laptop’s proxy settings.
Enter the Proxy Information: Set the proxy to 127.Zero.0.1 and the port to Fiddler’s port (generally 8888).
By manually configuring the browser’s proxy settings, you could seize visitors even without admin rights.

3. User-Level Proxy Settings
Some Windows versions allow users to set proxy settings on the consumer stage as opposed to the device stage. This may be finished by starting Internet Options > Connections > LAN Settings and configuring the proxy manually. As with the browser proxy configuration, set the proxy server to 127.Zero.Zero.1 with the suitable Fiddler port.
4. Using FiddlerScript for Specific Applications
FiddlerScript permits customers to create rules that regulate HTTP requests and responses. Even without admin rights, you can use FiddlerScript to check out and adjust traffic for unique packages that use configurable proxies. For instance, you can route only specific programs’ traffic through Fiddler by adjusting their network settings to apply the Fiddler proxy.
5. Avoiding HTTPS Decryption
One of the primary motives Fiddler calls for admin rights is to put in a root certificate, which lets it decrypt HTTPS visitors. If you are not able to put in this certificate because of admin restrictions, you can nevertheless use Fiddler to seize HTTP site visitors or analyze encrypted HTTPS visitors without viewing the contents. While this limits some functionality, it’s still beneficial for debugging certain kinds of issues.
Limitations of Using Fiddler Without Admin Rights
While the strategies above let you use Fiddler without admin rights, there are some obstacles you want to be privy to:
No System-Wide Traffic Capture: Without admin rights, Fiddler can’t modify gadget-wide proxy settings, meaning it could only seize traffic for unique applications in which you manually configure the proxy settings.
HTTPS Traffic: Without installing the foundation certificate, Fiddler would not be capable of decrypting HTTPS traffic, proscribing its usefulness for debugging steady net packages.
Limited to Browser-Based Traffic: In most instances, running Fiddler without an admin rights approach you’re restricted to shooting site visitors from web browsers or different configurable applications. Traffic from other packages that don’t allow proxy settings to be manually configured received’t be captured.
No Auto-Startup: Fiddler will no longer be capable of starting automatically with Windows, as this calls for modifying machine startup settings, which require admin rights.
Limited Functionality for Advanced Users: Advanced customers who depend on deep traffic inspection and manipulation (e.g., pen testers) may also discover the dearth of admin rights restrictive, mainly for intercepting HTTPS traffic.
Benefits of Using Fiddler Without Admin Rights
Despite the restrictions, there are several advantages to the usage of Fiddler in constrained surroundings:
Lightweight Debugging: By taking pictures best the site visitors you need, along with browser site visitors, you can nonetheless carry out most debugging tasks without admin rights.
Enhanced Security: Since you’re no longer putting in root certificate or editing device-extensive settings, there’s a lower risk of misconfigurations that could weaken device safety.
Portable Usage: Using a transportable version of Fiddler permits you to debug on any gadget without the want for installation.
Focused Traffic Analysis: By manually setting proxies only for specific applications, you can focus on analyzing traffic from those apps without capturing unnecessary system-wide data.
Read more information about here: The Net Worth of Charlie Chaplin: Exploring the Financial Legacy of a Silent Film Legend
Conclusion
Using Fiddler without administrator rights poses some challenges. However, it is still possible to perform thorough troubleshooting with the right settings. Whether you use the portable version of Fiddler, manually configure proxy settings. or avoid HTTPS decoding, you can still effectively record and monitor web traffic.
Although it has limitations in terms of capturing system-wide traffic and decoding HTTPS, Fiddler is a valuable tool for debugging browser-based applications and APIs in tight environments. By understanding these limitations and using creative solutions to immediate problems, You can still take advantage of Fiddler’s powerful abilities.
Frequently asked questions
1. Can I run Fiddler without administrator rights?
Yes, you can run Fiddler without administrator rights by using the portable version or by manually configuring your browser or application proxy settings. However, some features such as receipt logging System-wide data transmission, and HTTPS decryption may be limited.
2. How do I configure my browser to apply Fiddler without admin rights?
You can manually set the proxy settings for your browser (e.g., Chrome, Firefox, Edge) to route visitors through Fiddler by placing the proxy server to 127.0.Zero.1 and the appropriate port (commonly 8888).
3. Can I seize HTTPS site visitors with Fiddler without admin rights?
Capturing HTTPS traffic without admin rights is confined because Fiddler can’t install its root certificates to decrypt traffic. However, you could still capture encrypted HTTPS traffic, although you may not be capable of investigating the content.
4. What are the limitations of the use of Fiddler without admin rights?
Some boundaries include the inability to seize device-huge traffic, restrained HTTPS decryption competencies, and guide proxy configuration for specific programs.
5. Is there a portable model of Fiddler?
While Fiddler does not officially provide a portable version, customers can create one by using copying the installed documents from a system with admin rights and jogging it on the target machine without requiring installation.
-

 Blog11 months ago
Blog11 months agoGuia Silent Hill Geekzilla: Your Ultimate Guide
-

 Business10 months ago
Business10 months agoPikruos.com: Your Premier Destination for Creative Visuals
-

 health8 months ago
health8 months agoWhat is Pollaste? Review Details
-

 Technology11 months ago
Technology11 months agoElevating Your Data Game with SSIS 816
-

 Blog9 months ago
Blog9 months agoComplete Insights About The Topic in Gloriando 2024
-

 Education10 months ago
Education10 months agoTickzoo.info: Your Go-To Guide for Trending Topics and Information
-

 Business10 months ago
Business10 months ago2024 Vision: Innovative Marketing Strategies for Insurance Companies
-

 Education10 months ago
Education10 months agoDiving into the Forbidden: Kristen Archives Taboo Collection


